2024 Manufacturing Leadership Award Finalists Recognized for Achievements in Smart Factories, Sustainability, AI and More
June 5 gala will recognize companies and individuals that are leading digital manufacturing transformation
Washington, D.C. – The Manufacturing Leadership Council, the digital transformation division of the National Association of Manufacturers, today revealed the list of world-class manufacturing companies and individual leaders recognized as finalists for the 2024 Manufacturing Leadership Awards, the 20th season of the industry’s premier awards program for achievements in digital manufacturing.
“More than ever, manufacturers are finding that digital technology investment is good for business as they achieve new levels of performance in efficiency, productivity and innovation,” said MLC Founder, Vice President and Executive Director David R. Brousell. “The finalists that we are recognizing for this year’s awards have demonstrated not just the business benefit of Manufacturing 4.0 technology, but also a fresh and imaginative approach to applying it in a transformative way.”
The 2024 awards feature nine project categories to recognize company achievements in the areas of Artificial Intelligence and Machine Learning; Collaborative Ecosystems; Digital Network Connectivity; Digital Supply Chains; Engineering and Production Technology; Enterprise Integration and Technology; Operational Excellence; Sustainability and the Circular Economy; and Transformational Business Cultures. Additionally, individual leaders are recognized in the Digital Transformation Leadership and Next-Generation Leadership categories. Award nominations were judged by a distinguished group of manufacturing leaders from across the industry.
“Each year, we see entries from manufacturers of all sizes, from a wide mix of industries and from locations around the world all telling different versions of the same story: digital is transformational,” said MLC Senior Content Director Penelope Brown, who is head of the awards program. “The quality and sophistication of this year’s award entries were outstanding. Many projects demonstrate how M4.0 investments are positioned for significant business model improvements. Additionally, the individuals recognized in the Digital Transformation Leadership and Next-Generation Leadership categories are exemplary leaders now and for the future.”
Select award winners will present their projects at the MLC’s Rethink Summit, which will take place at the JW Marriott Marco Island Beach Resort in Florida June 2–5. Rethink, also now in its 20th year, is the industry’s leading event for exploring manufacturing’s digital era. Details are available here.
“This year’s program will examine the past, present and future of digital manufacturing, and we are proud that the MLC has had an important role in building a community of leaders and organizations that are leading the charge,” Brousell said. “Whether this is your first time at Rethink or your 15th, you will always come away with new connections, new aspirations and new ideas that you can implement right away.”
All finalists will be recognized onstage at the Manufacturing Leadership Awards Gala, following the Rethink Summit, on Wednesday, June 5, at 7:00 p.m. EDT. Also to be announced at the gala will be category winners for all project and individual categories, winners of the Manufacturing in 2030 Award, the Manufacturing Leader of the Year, the Small/Medium Enterprise Manufacturer of the Year and the Large Enterprise Manufacturer of the Year. See a complete list of finalists here.
Nominations for the 2025 Manufacturing Leadership Awards will open in September.
-MLC-
Founded in 2008 and now a division of the National Association of Manufacturers, the Manufacturing Leadership Council’s mission is to help manufacturing companies transition to the digital model of manufacturing by focusing on the technological, organizational and leadership dimensions of change. With more than 2,500 senior-level members from many of the world’s leading manufacturing companies, the MLC focuses on the intersection of advanced digital technologies and the business, identifying growth and improvement opportunities in the operation, organization and leadership of manufacturing enterprises as they pursue their journeys to Manufacturing 4.0.
MLC Announces Manufacturing Leadership Award Finalists

The Manufacturing Leadership Council, the NAM’s digital transformation division, has announced the 2024 Manufacturing Leadership Awards finalists.
About the awards: Now in their 20th season, the Manufacturing Leadership Awards
honor the most outstanding manufacturing companies and their leaders for groundbreaking use of advanced manufacturing technology.
- This year’s program features nine project categories, including Artificial Intelligence and Machine Learning, Digital Supply Chains and Sustainability and the Circular Economy.
- It also includes two categories for individuals: Digital Transformation Leadership for executive-level manufacturing leaders and Next-Generation Leadership for up-and-coming leaders age 30 and under.
How we decide: Nominations are judged by an outside panel of digital manufacturing experts with deep industry knowledge and experience.
- For project entries, judges assess an initiative’s effect on improving manufacturing processes, furthering business goals and advancing company strategy, as well as how much digital technology the project used.
- For individual nominations, judges look at each person’s impact both inside and outside their organization, and whether they meet the criteria as a role model for other manufacturing leaders.
Celebration and ceremony: Winners for both of these categories will be announced at the Manufacturing Leadership Awards Gala on June 5 at the JW Marriott Marco Island Beach Resort.
- Award finalists will also be recognized, as will winners of the Manufacturing in 2030 Award, the Manufacturing Leader of the Year, the Small/Medium Enterprise Manufacturer of the Year and the Large Enterprise Manufacturer of the Year.
- The gala caps off Rethink, the industry’s leading event for accelerating digital transformation. (Rethink also takes place in Marco Island, June 2–5.)
The last word: “More than ever, manufacturers are finding that digital technology investment is good for business as they achieve new levels of performance in efficiency, productivity and innovation,” said MLC Founder, Vice President and Executive Director David R. Brousell.
- “The finalists we are recognizing for this year’s awards have demonstrated not just the business benefit of Manufacturing 4.0 technology, but also a fresh and imaginative approach to applying it in a transformative way.”
Welcome New Members of the MLC April 2024
Introducing the latest new members to the Manufacturing Leadership Council


Philippe Adam
CMO
aPriori
![]()
www.apriori.com
![]()
https://www.linkedin.com/in/philippeadam1/

Kevin Carpenter
Chief Supply Chain Officer
Toro

www.toro.com
![]()
https://www.linkedin.com/in/kncarpenter/

Rob Harlow
Senior Manager, NA Production Engineering & Automation R&D
DENSO
![]()
https://www.denso.com/us-ca/en/
![]()
https://www.linkedin.com/in/rob-harlow-b1b55887/

Brad Larson
Director of Manufacturing
Fey Industries, Inc.
![]()
https://www.feyindustries.com/
![]()
https://www.linkedin.com/in/brad-larson-3b4b63145/

Pete Millett
Director – Global Engineering and Manufacturing Director
Lubrizol

www.lubrizol.com
![]()
https://www.linkedin.com/in/pete-millett-0ab50711/

Lion Moeliono
Global Manager, Digital Manufacturing Transformation & Innovation
Rockwell Automation
https://www.rockwellautomation.com/en-us.html
![]()
https://www.linkedin.com/in/lion-moeliono-0058752/

Raja Shembekar
Vice President Manufacturing & Corporate Officer
PACCAR

https://www.paccar.com/
![]()
https://www.linkedin.com/in/raja-shembekar-06934ba8/

Balthazar Moncada
Director of Operations | COO
HELVEX

https://www.helvexusa.com/
![]()
https://www.linkedin.com/in/baltazar-moncada-rodriguez/

Hugo Alberto Gomez Sierra
CEO
Condumex
https://condumexinc.com/
![]()
https://www.linkedin.com/in/hugo-gomez-a2370011/
The Road to Digitalization: Evaluating Readiness for Digital Transformation

Manufacturers should employ a comprehensive assessment framework to identify strategic actions required to achieve a higher level of digital maturity.
TAKEAWAYS:
● Manufacturers that stand still run the risk of falling behind.
● The insights are in the data, fueling the continuous improvement cycle, where each step reveals new opportunities for innovation and optimization.
● Measuring digital maturity is the catalyst for the transformative process.
The fourth industrial revolution has driven the manufacturing industry to an inflection point where technological advancements are no longer just accelerators for growth but fundamental for organizational survival. This digital shift is not merely about adopting new technologies—rather it is about realizing a profound change in how organizations operate, innovate, and deliver value. As leadership focuses on finding a strategic balance between technological advancements to realize quick, tangible benefits while maintaining the flexibility to scale operations in an increasingly complex environment, one thing remains constant—namely, the insights are in the data and the ability to assess an organization’s preparedness for digitalization is paramount for success.
Redefining Readiness: A Fresh Perspective to Drive Transformation Differently
Of the many manufacturers that have started their digital transformation journey, relatively few have realized the value they aimed to achieve, often because they are simply starting in the wrong place. Building the future factory involves visionary leadership and practicality, beyond just adopting new technologies for quick changes. Leaders must envision their organization’s future, not by predicting technologies, but by understanding industry directions, their starting point, and the competitive path forward. This intersection of industry trends, current state, and defined organizational objectives, gives birth to an organization’s unique digitalization strategy—underscoring digital readiness and representing a holistic approach that integrates the technological, cultural, and operational facets of an organization to derive true digital value.
A McKinsey & Company study highlights the significance of digital readiness and understanding one’s digital maturity and indicates that companies that excel in their digital transformation efforts are twice as likely to report double-digit growth rates compared to their less-prepared counterparts (McKinsey 2020). But, with their enthusiasm for technology adoption and their emphasis on strategic planning, many manufacturers overlook assessing digital maturity and the readiness of current systems to integrate with new technologies.
Digital maturity denotes the sophistication with which an organization incorporates digital technologies and methodologies across its operational frameworks, customer engagement strategies, and innovation initiatives. This concept evaluates several dimensions, including the automation level and digitization depth of core business workflows, the strategic application of data analytics for enhanced decision-making processes, and the comprehensive integration of advanced digital technologies such as robotics, artificial intelligence (AI), and the Internet of Things (IoT) within the enterprise ecosystem.
“A digitally mature enterprise can be characterized by its advanced integration of technology across all facets of its operations.”
Through this rigorous exercise, leaders can identify the most critical technologies and processes that will provide the quick win, tackle the most prominent operational deficits, drive alignment of their operational goals, and serve as a foundation for future scalability. Using this information as a baseline, you can shape your digital transformation strategy from a simple shopping list of the latest technologies and transform it into a more comprehensive road map that addresses the gaps and leverages the existing strengths of existing operations.
Digital Mastery: Key Indicators of an Advanced Organization
In its 2023 Manufacturing Horizon Report, CRB revealed that companies effectively integrating the right technologies with their operational dynamics have experienced a surge in productivity by an astounding 27 percent, and a subsequent reduction in operational costs by nearly 19 percent. A study by Deloitte shows companies at the highest level of digital maturity are 26 percent more profitable than their industry averages.
A digitally mature enterprise can be characterized by its advanced integration of technology across all facets of its operations. From strategic decision-making to day-to-day processes, such organizations leverage digital tools and platforms to enhance productivity, foster innovation, and deliver superior customer experiences. Central to their operational model is the use of data analytics and AI to drive business insights, ensuring agility and responsiveness to market changes while simultaneously prioritizing cybersecurity and data privacy, embedding these considerations into their technology architecture and everyday business practices.
But digital maturity is not just about technology adoption, it’s about transforming organizational behaviors and business models so they can thrive in the digital age (Deloitte 2020; McKinsey & Company 2021). In these organizations, essential operations are no longer confined to isolated departmental units—rather they are developed and overseen by interdisciplinary, production-focused teams with well-defined performance standards and business objectives. The most technologically advanced organizations possess the infrastructure to facilitate comprehensive platform-based procedures, bolstered by self-sufficient resources at the forefront. These cross-functional teams are at the core of cultivating the next generation of manufacturing culture: they consistently provide scalable, technology-led solutions, products, or client experiences, fueled by a continuous cycle of learning and innovation that stimulates regular advancements and enabling them to adapt swiftly to evolving client expectations. and driving their competitive edge.
From Traditional to Transformed: The Path to Digital Maturity in Manufacturing
Navigating the intricate journey towards digital maturity requires a sophisticated understanding of the evolutionary stages that manufacturing entities must traverse. Leading industry consultants have highlighted delineated frameworks that categorize such progression within manufacturing environments. While each has their own interpretation, these stages, broadly outlined, transition from initial digital awareness, where the digital strategy is nascent and fragmented, through to a fully integrated digital ecosystem, characterized by advanced analytics, IoT implementation, and AI applications. This progression encapsulates a journey from foundational digital capabilities towards a transformative state, where digital technologies are leveraged not just for incremental improvements but are deeply embedded into the fabric of operational processes and strategic visions, driving innovation, efficiency, and competitive advantage in a connected, smart manufacturing landscape.
“Navigating the intricate journey towards digital maturity requires a sophisticated understanding of the evolutionary stages that manufacturing entities must traverse.”
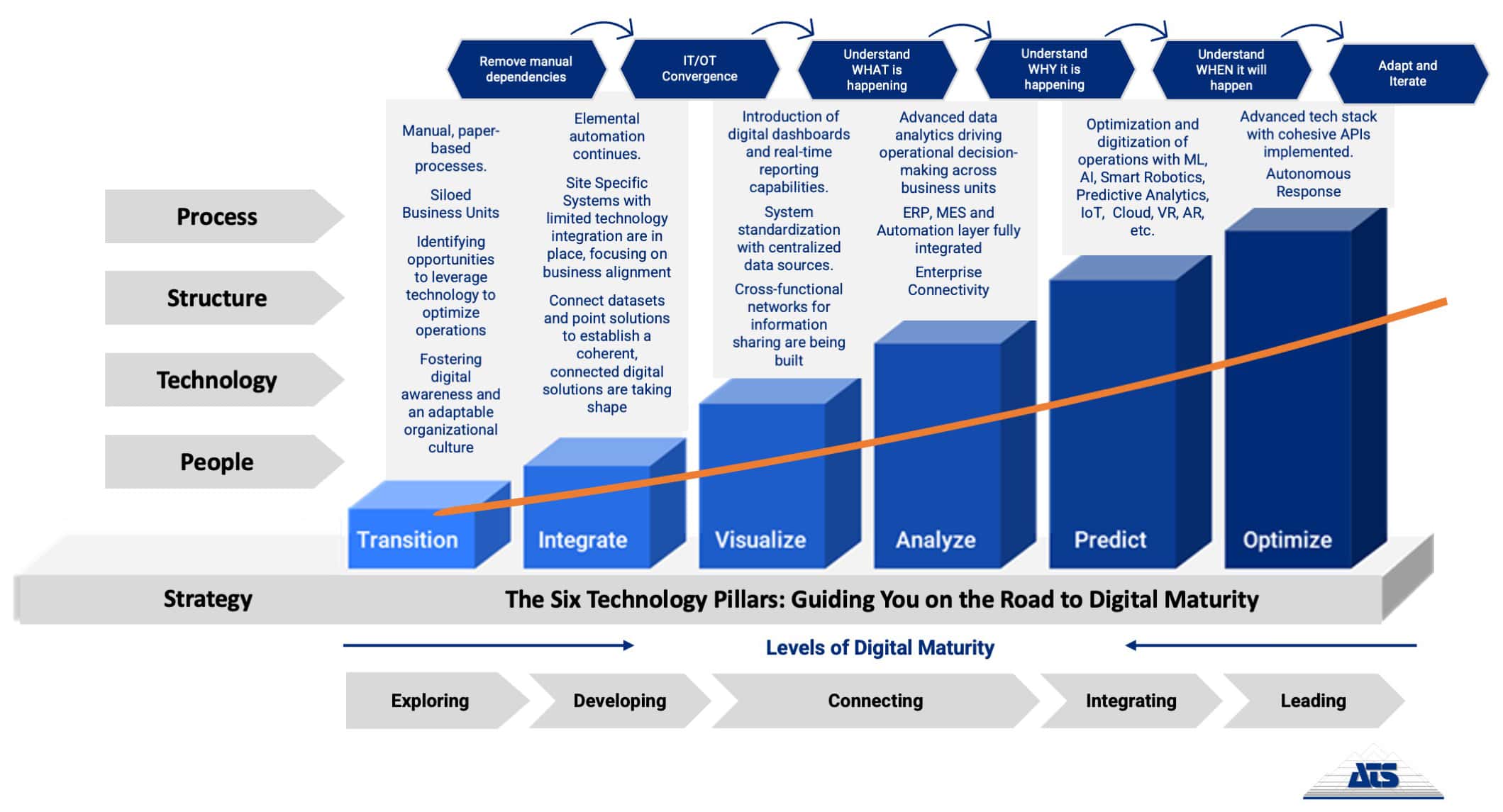
Coupled with such widely recognized industry knowledge, our real-world experience has driven the creation of a digital maturity methodology that emphasizes a people-first, technology-enabled approach, focusing on the strategic deployment of technology to deliver real business value. By identifying areas for maturity enhancement within organizational and technological domains (OT/IT), we facilitate the transition towards a fully optimized manufacturing solution. Central to our process are six key technology pillars that support digital manufacturing advancements, employing an iterative transformation lifecycle that incorporates analysis and feedback after each phase to refine processes and improve data collection (Figure 1). This ensures a continuous loop of improvement and adaptation, aligning technology implementation with human insight and collaborative engagement.
Figure 1: The path to digital maturity
Metrics of Modernization: Maturity and Momentum
Quantifying an organization’s digital maturity involves a systematic approach. This approach includes evaluating the integration and effectiveness of existing digitization across all business units and providing leaders with a clear understanding of their current position in their digital transformation journey, while simultaneously outlining the path toward achieving higher levels of technological integration and operational efficiency. This multi-dimensional assessment includes an analysis of several key factors: digital strategy formulation, leadership commitment towards digital initiatives, operational agility for adopting new technologies, the level of client engagement through the digital ecosystem, and the empowerment of the workforce with digital tools and skills. This measurement not only benchmarks an organization’s current capabilities against industry standards and best practices, it also identifies gaps and areas for improvement, facilitating targeted investments in technology, processes, and workforce development, strategically allocating resources for digital growth. Ultimately, the measurement accelerates an organization’s transformation into future-proof, digitally mature enterprises that are more competitive, thereby fostering a culture of digital excellence that is adaptive in the rapidly evolving digital landscape.
While many recognize that the ability to measure maturity is a powerful catalyst for change, it can be challenging to successfully quantify relevant insights. From a broad perspective, effective metrics to provide granular insight into three specific dimensions of transformation:
Technology:
- Overall equipment effectiveness is a critical metric for measuring manufacturing efficiency, combining performance, availability, and quality.
- Percentage of connected assets: Quantify the scale of IoT implementation, the degree of automation, and the existing adoption of advanced technologies.
- Data capture rate: Measure the breadth of real-time data collection for analytics.
Process:
- Data-driven decision-making capabilities in production, planning and scheduling, inventory management, and integrated supply chain management. This includes examining lead times and cycle times to track gains in agility and responsiveness; evaluating inventory turnover ratio to measure supply chain optimization and risk reduction; and studying first-pass yield to track improvements in quality control aided by data analytics.
- Workflow optimization for efficiency and agility.
Organization:
- Leadership commitment to digital transformation and strategic alignment, including a digital skills index to evaluate workforce digital literacy.
- Cross-functional collaboration enabled by technology platforms that quantify cross-functional project success rates and collaboration effectiveness.
- Cybersecurity, data governance, and risk management protocols in place to expose vulnerabilities or inadequate practices, including cybersecurity Posture Assessment
Organizations can adopt various frameworks and/or maturity models to systematically evaluate and benchmark their digital progress against parameters, enabling a structured roadmap for digital advancement. We highlight several frameworks organizations could use for a structured assessment approach:
- Smart Industry Readiness Index (SIRI): EDB’s framework provides a rigorous 16-dimension assessment. The Prioritization Matrix (TIER) facilitates targeted action based on today’s state, impact to the bottom line, essential business objectives, and references to the broader community.
- Acatech Industrie 4.0 Maturity Index: This model uses a stage-based approach to help organizations chart their maturity progression and define their developmental trajectory.
- Digital Maturity Models (Deloitte, BCG, CESMII, etc.): These consultancy frameworks offer broader enterprise-level assessments, aiding strategic alignment.
In my experience, the journey to digital maturity demands an honest assessment of your organization’s current standing. By adopting any of the proven frameworks and critically analyzing the data, manufacturing leaders gain a diagnostic blueprint for targeted action. This process uncovers the specific investments in technology, process optimization, and workforce development that will yield the highest return, transforming the framework from a mere scorecard into an instrument of strategic change by creating the business case for your continuous improvement initiatives.
Charting the Course: Evaluating Progress Towards Digital Excellence
Given the dynamic ecosystem of the manufacturing industry—characterized by fluctuating demand, raw material availability, and geopolitical uncertainties—the ability to effectively scale a technology strategy and advance your digital maturity is tantamount to achieving operational agility and sustained growth. Scaling is not merely a replication of solutions that have demonstrated value in a small-scale setting; it is an intricately planned endeavor that aligns technology with business objectives, regulatory frameworks, and workforce capabilities. Contrary to popular belief, it does not merely refer to deploying more of the same technology across an enterprise. It involves understanding the contextual intricacies of each operational environment and adapting the foundational strategy to the idiosyncrasies accordingly.
“By strategically leveraging assessment frameworks and focusing on actionable insights, manufacturing leaders gain a powerful tool for continuous improvement.”
For instance, a mid-sized automotive supplier improved operations by using a digital maturity assessment, which identified a gap in data analytics. By investing in IoT sensors and cloud analytics, they reduced downtime by 15 percent, improved efficiency by 8 percent, and fostered a proactive maintenance culture. Similarly, a large food and beverage company enhanced its complex supply chain visibility and efficiency through a maturity assessment, adopting cloud and IoT technologies to improve delivery rates, reduce inventory costs, and ensure food safety. These examples underscore the value of data-driven decisions and targeted strategies in driving continuous improvement, innovation, and resilience against technological disruptions and evolving market demands, highlighting the importance of a culture of innovation integrated into operational practices.
This path toward digital maturity is an ongoing journey, not a single destination. The importance of understanding where to begin extends beyond the immediate advantages of implementing technology, nurturing a manufacturing sector that is both resilient and visionary. By strategically leveraging assessment frameworks and focusing on actionable insights, manufacturing leaders gain a powerful tool for continuous improvement. This approach equips organizations with the capability to adeptly confront the challenges and seize the opportunities that emerge in the digital era, driving their long-term competitiveness and adaptability, purposely and efficiently. The ultimate reward, however, lies not just in achieving a higher maturity score, but in building a manufacturing enterprise that will thrive in the dynamic industrial ecosystem.
About the author:

Holly Becker is director of Commercialization at ATS Applied Tech Systems, LLC.
For Manufacturers, Digital Maturity Hasn’t Yet Come of Age

Manufacturers are at an early stage of understanding how far advanced they are with Manufacturing 4.0, as they grapple with linking digital strategy to business strategy, cultural and organizational issues, and leadership development challenges.
KEY TAKEAWAYS:
● A majority of manufacturers either do not have a formal process for digital maturity or do informal benchmarking.
● A majority of manufacturers have a digital maturity target of Manual Execution with Digital Support, with an equal balance of companies feeling like they are on track or behind schedule.
● Digital strategy, in general, is still poorly integrated with overall business strategy, capital strategy, supplier decisions, and M&A strategy yet remains vital towards future competitiveness.
As companies continue to share feedback that they are either not seeing value from digital transformations or are feeling like they are behind schedule, MLC fielded a new survey to understand how companies are managing digital maturity. Having clear criteria for success is important for any transformation journey, and the survey results show that manufacturers are just starting to put in place formal metrics for assessing their maturity.
Manufacturers continue to focus on building the core foundation of Manufacturing 4.0 through technology investments and workforce development. However, in order to become digitally mature, what’s required is a deeper integration of Manufacturing 4.0 with the rest of manufacturers’ business processes. Additionally, to overcome the cultural barriers facing digital transformation, leadership teams need to be more committed to their own development and active engagement in this change.
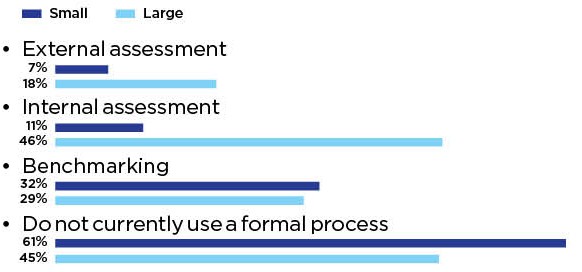
Section 1: Measuring Digital Maturity
Measurements of digital maturity are not yet universally defined, which leads to variation in how companies understand their current maturity level. Currently, roughly 10% of manufacturers (across both SMM and large companies) do a formal external assessment against some sort of defined standard. Roughly 30% (again, for both SMM and large) do external benchmarking. With regards to internal assessments, however, there is a significant difference, with roughly 46% of large manufacturer respondents doing internal assessments across factories. Most large manufacturers that conduct any sort of assessment do so through a combination of assessments, while most SMMs do only one type of assessment. Overall, however, roughly 50% of total respondents do not have any formal process by which maturity is assessed.
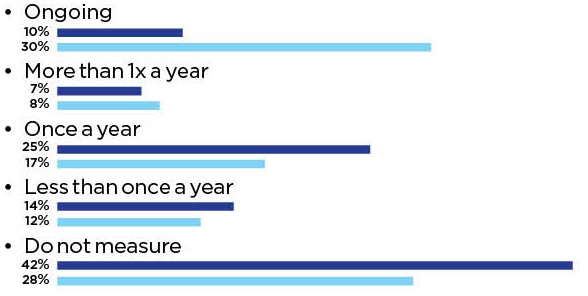
This lack of a formal process is validated by the frequency in which assessments are done. For SMMs, the majority of companies that do assessments do so once a year or less. For large manufacturers, it is roughly split between ongoing assessments and once a year or less.
Finally, there is a difference in the business metrics that align with digital maturity. For SMMs, the focus is on customer and employees (on-time delivery, product quality, and employee satisfaction are in the top 5), while large manufacturers are focused on traditional operational metrics (cost savings, OEE, and productivity are in the top 5).
1. Digital Maturity is Still a Feeling vs. a Quantifiable Metric
Q: How does your company measure digital maturity?
2. Few Link Maturity Measurements to Formal Planning Cycles
Q: How often do you measure digital maturity
3. SMMs Leverage Customer and Employee KPIs, While Large Firms Rely on Traditional Operational Metrics
Q: What business KPIs are used specifically to measure digital maturity?

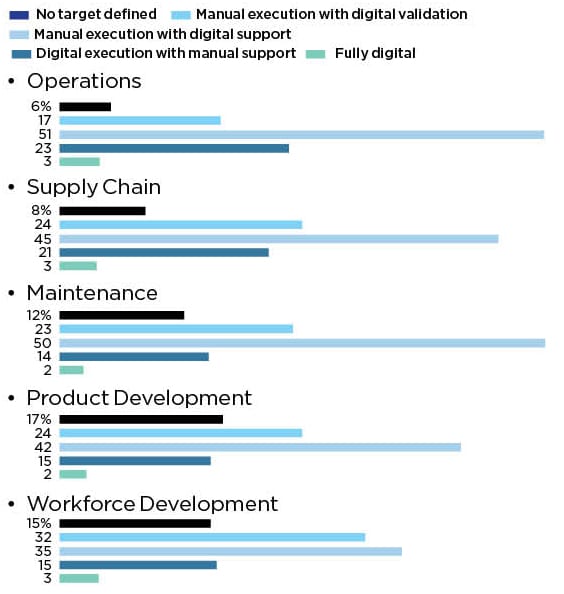
When looking across various aspects of the business, survey results show consistency between SMM and large manufacturers when it comes to digital maturity target, progress, and peer competitiveness. The digital maturity targets for operations and supply chain reflect normal distributions, centered around a level 2 – manual execution with digital support. For maintenance, product development, and workforce development, the results indicate left-centered distributions, with more companies targeting lower maturity levels than for operations or supply chain.
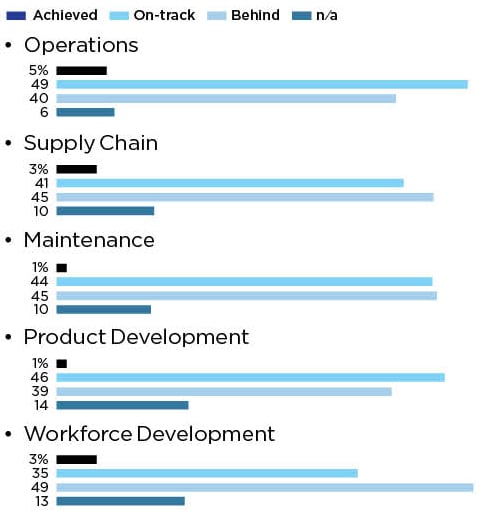
Digital progress versus target is relatively consistent across all processes, with an even distribution between on-track and behind schedule. The biggest gap in progress is around workforce development.
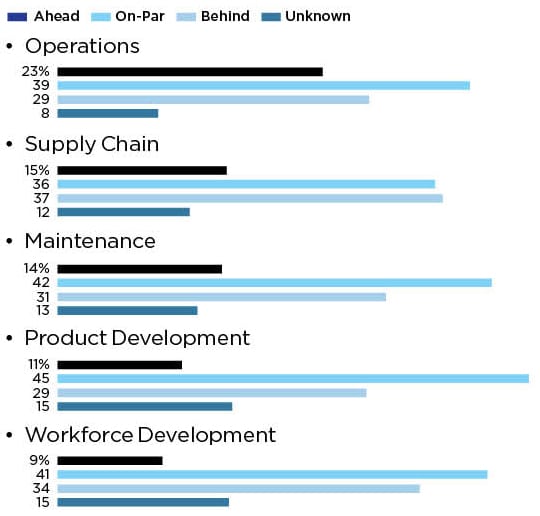
Finally, when comparing to peers, survey respondents indicate a difference in perception, especially around operations, with 23% of respondents feeling they are ahead of their peers. As with their internal view of progress, the area where companies feel they are further behind their peers is around workforce development.
4. Digital Maturity Targets Reflect the Challenges of Transformation
Q: How would you assess you digital maturity TARGET?
5. Project Success Guides Progress
Q: How would you assess your digital maturity LEVEL vs. TARGET?
6. Peer Assessments a Mixed Bag
Q: How would you assess your digital maturity vs. your PEERS?
Section 2: Digital, Business Strategy Integration Lacking
When looking at how digital transformation strategy is integrated with other business strategies, there is quite a bit of variability, with the weighted average relatively low. On a scale of 0-10 (with 10 being highly integrated), the survey results peg overall business strategy and capital investment strategy at ~3.3. The integration with M&A, partnerships, and supplier decisions is less at ~2.5. However, the overall importance of digital maturity towards future competitiveness is ~4.7.
This validates the need for integration of digital projects in all aspects of the business as critical for digital maturity growth.
7.Strong Influence of Digital Maturity on Competitiveness
Q: How well does your smart factory strategy integrate / influence the following?
1 (low integration / importance) – 10 (high integration / importance)

Section 3: A Need for Greater Leadership Knowledge
Leadership plays a critical role in corporate culture. As culture continues to be identified as a key driver for digital transformation success, the data demonstrates a validation of the need to continue to focus on developing leadership knowledge and skills with the same rigor as front-line workers. Two-thirds of respondents feel that leaders are knowledgeable about Manufacturing 4.0 but are in need of external guidance to effectively lead transformation efforts. Additionally, 20% are uninformed and in need of significant support. What was interesting in the results is that C-suite leaders who responded ranked themselves as less informed than other respondents. This awareness is an important step towards improving their knowledge and skills.
An important step in developing their skills and knowledge is to incorporate Manufacturing 4.0 topics into their regular learning and development program. Only 20% of respondents felt that this currently in place, while over 60% felt learning was either ad-hoc or nonexistent.
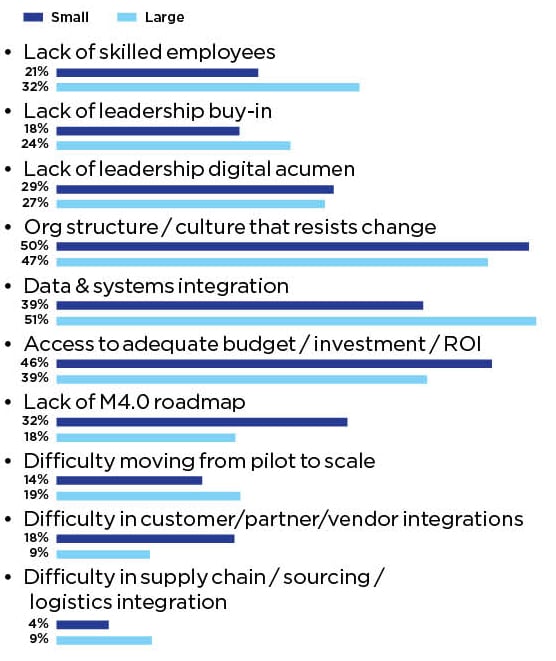
These findings are further validated when looking at the roadblocks to improving digital maturity. Organization structure / culture that resists change and leadership digital acumen, along with a skilled workforce and leadership buy-in, were listed as top barriers for both SMM and large manufacturers.
Where a delta was seen in roadblocks (although all of these items were important) was large manufacturers identifying data and systems integration as critical and SMM companies identifying investments / access to budgets and an M4.0 roadmap as critical. M
8. Greater Leadership Learning Needed
Q: Digital acumen of company’s senior leadership team.
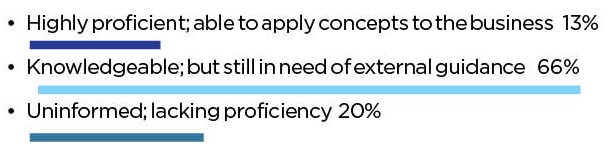
9. M4.0 Needs to Be Embedded in Formal L&D Programs
Q: How often does the senior leadership team engage in active learning around digital transformation?
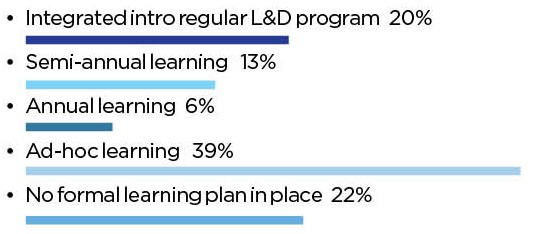
10. Organizational Structure, Culture Remain Top Roadblocks
Q: What do you feel are your company’s primary roadblocks to improving your digital maturity?
About the author:

Steven Moskowitz, Ph.D., is the Senior Director, Event Content at the Manufacturing Leadership Council.
GenAI Ushers Human-Like Intelligence in Manufacturing

Catalyzing Digital Maturity with Generative AI: Democratizing Data Analysis, Automation, and Problem-Solving in Manufacturing
TAKEAWAYS:
● Generative AI stands as a transformative technology poised to democratize data analysis, reasoning, and automation throughout the manufacturing industry’s value chain.
● Leveraging Retrieval Augmented Generation to enhance foundational models represents an optimal technique for beginning to harness GenAI’s value.
● Manufacturers should evaluate digital maturity and initiate pilot-testing applications to identify high-impact, feasible business challenges while establishing an interconnected and contextualized data foundation.
The AI Wave in the Manufacturing Industry
The AI wave, and specifically, Generative AI (GenAI), is poised to disrupt manufacturing. GenAI’s greatest strength lays in democratizing the power of data analysis and automation through a reasoning engine and a natural language interface. A 2023 BCG survey of 1,800 manufacturing executives found that GenAI is the technology with the most disruptive potential1. With the power of large data analysis, manufacturers can optimize value systematically and dynamically — a feat of “mission impossible” proportions today.
AI Categories and Capabilities
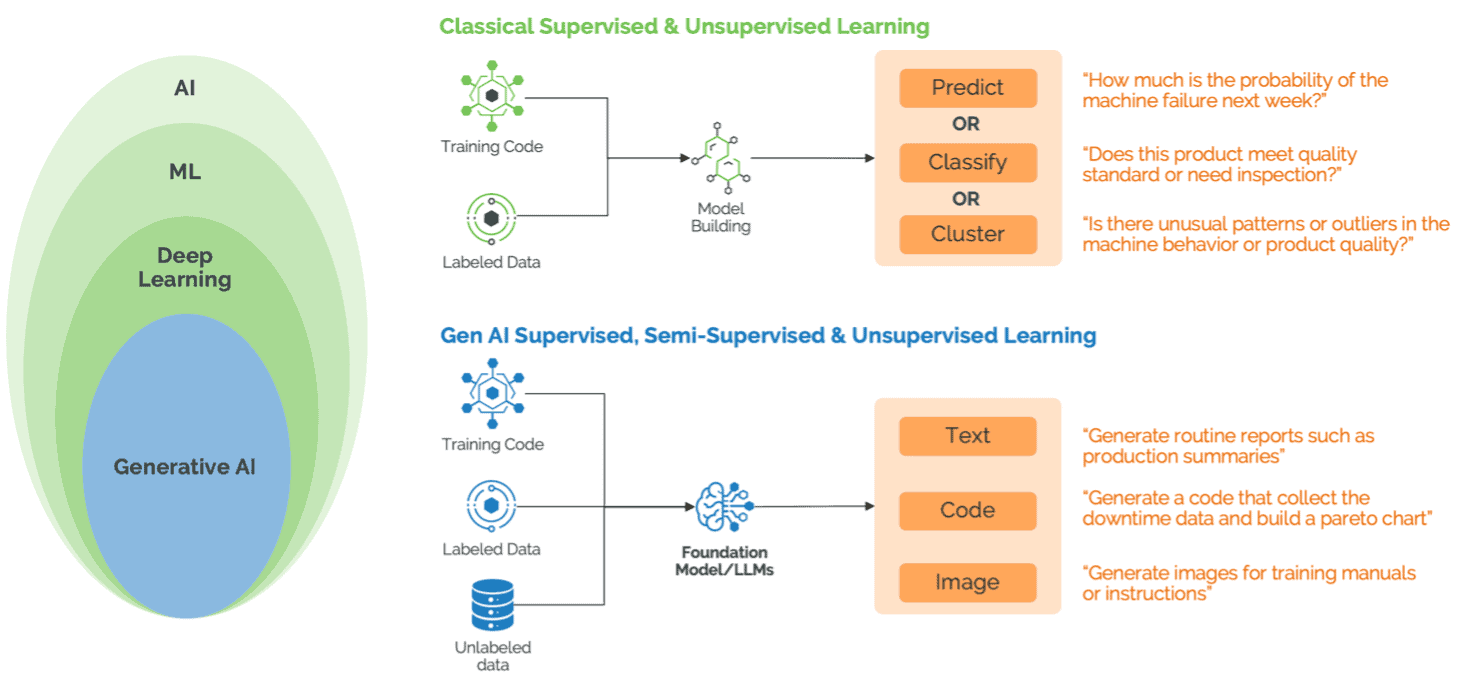
Figure 1: AI Types and Capabilities
In the last few years, classical machine learning has been broadly implemented in manufacturing to predict machine failures, classify defects, identify process outliers in machine behavior and product quality, and even to autonomously adjust machine parameters to optimize quality and throughput. While classical machine learning has been a staple, the exploration and implementation of GenAI’s capabilities in this sector are just beginning to unfold. Both classical machine learning and GenAI are valuable for different reasons. GenAI revolutionizes data analytics by pre-training on vast unstructured datasets, making it possible to alter the way that prediction, classification, and clustering are calculated in classical machine learning models. Meanwhile, GenAI’s natural language processing and code generation/interpretation capabilities allow business professionals to access complex data analysis without needing programing or data science expertise. The development of multimodal foundation models is unlocking capabilities to turn not only text but also audio, images, and video into dynamically generated insights in the hands of frontline workers. Mexican workers can benefit from the problem-solving experiences of their Asian and Polish counterparts, aided by an intelligent agent that offers summarized solutions and specific action recommendations based on insights from these regions. Industrial engineers can scan the timetable or Standard Operating Procedures (SOP) on paper to generate digital SOP and work instructions and associate them with the product and process design.
AI and Generative AI Use Cases for Manufacturing
GenAI’s adoption will democratize access to vast reservoirs of structured and unstructured knowledge bases, enable large-scale data analysis, and provide powerful reasoning engines and complex problem-solving capabilities to all individuals, regardless of their technical background. Ultimately, manufacturers can use these capabilities to mimic the adaptive problem-solving capabilities of humans, by learning behavioral patterns from past human and machine experiences. Gartner refers to this as Actionable AI and sees it as one of the top innovative technology trends for manufacturing operations leaders4.
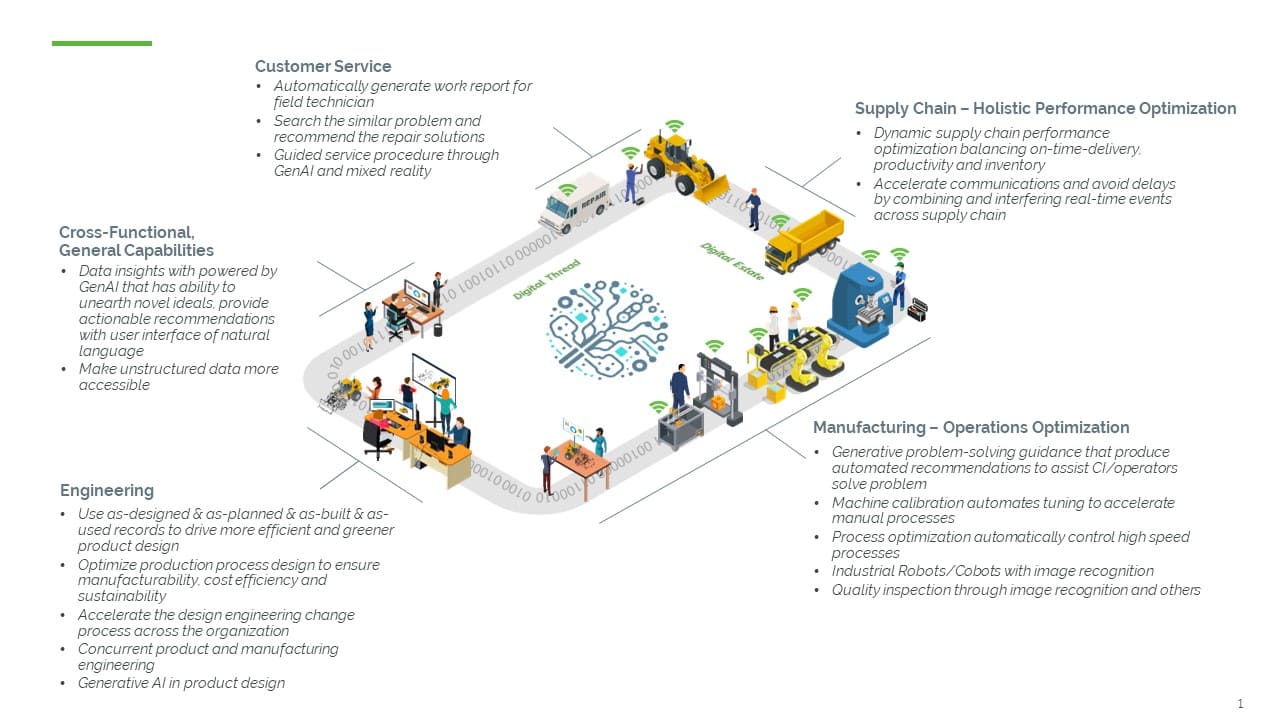
Figure 2: Classical ML and Generative AI use cases across value chain2
Data Insights: Empowering the Entire Value Chain
From engineers to shop floor personnel, GenAI is revolutionizing data analysis. It scales insights from both internal and external, particularly unstructured, data sources — enriching advanced analytics with foundational model-generated insights. GenAI’s true innovation in data insights lies in its ability to unearth novel ideas, offer an unlimited scope to dissect data from multiple perspectives, and provide actionable recommendations — not just diagnostics — all in real-time.
Operations Optimization: A New Paradigm for Operations Leaders, Frontline Workers, and Continuous Improvement (CI) Leader
GenAI introduces closed-loop asset optimization by supplementing programmable logic controller (PLC) inputs with a broader spectrum of data points like vibrations, temperature, and pressure (typically captured from IoT sensors). As a result, operations leaders can leverage GenAI to pinpoint machine optimization opportunities. Furthermore, frontline workers and continuous improvement leaders can consult GenAI systems for advice on specific operational challenges — eliminate bottleneck and non-value-added activities — transforming GenAI into a ubiquitous and invaluable partner in continuous improvement.
Product and Process Design Optimization: For Innovative Product and Manufacturing Engineers
In addition to generative design, product engineers can utilize GenAI for product design by integrating multifaceted data from as-designed and as-built and as-used records, leading to smarter and more efficient design choices. Manufacturing engineers can employ GenAI for process design optimization, ensuring that manufacturability, cost-efficiency, and sustainability are embedded at the very heart of production processes. Through GenAI, design principles are not just informed by data but are fundamentally driven by the most advanced insights available. GenAI can also help accelerate the collaboration and engineering change process across the organization by leveraging contextual information from otherwise untapped information sources like historical paper-based designs, and by securing inputs from a globally distributed design team in their natural languages.
Holistic Performance Optimization: Strategizing for Supply Chain and Operations Leaders
Supply chain and operations leaders have long grappled with the complex challenge of dynamic performance management, balancing safety, quality, delivery, productivity, and inventory. GenAI excels in parsing large, complex, and interlinked datasets, learning from historical patterns to offer insights and recommendations for emerging issues, equipping leaders with a robust tool for strategic decision-making. By combing real-time updates (both internal and external; for example, weather and frequently changing geo-political landscape) and inferring the impact to shipment updates as communicated via email from suppliers, GenAI copilots can accelerate communication across the supply chain thereby shortening delays and making the operations more responsive and resilient.
The Approach for GenAI in Manufacturing
In theory, industrial companies can approach Generative AI in three ways: training their proprietary foundation model, fine-tuning an existing foundation model, or enhancing an existing model via prompt engineering and Retrieval Augmented Generation (RAG). Prompt engineering refers to the process of designing, refining, and optimizing input prompts to guide a generative AI model toward producing desired outputs3. RAG is an architecture that augments the capabilities of a Large Language Model (LLM) by adding an information retrieval system that provides grounding data. In practice, training proprietary models and fine-turning foundation models are both resource intensive and can quickly run up costs in the of tens of millions of dollars — leaving most manufacturers with very unclear ROI. RAG alongside prompt engineering is the least expensive and quickest method. It also offers greater transparency as it can refer to sources, making it an ideal starting point for companies looking to explore GenAI technology and validate use cases.
With foundational models and RAG frameworks improving with strong reasoning capabilities and tools, we can expect the adoption of GenAI to scale quickly — roles across the value chain will be enabled by one or multiple copilots. In fact, the simplest RAG application can be built with as little as “five lines of code”5. However, regardless of the techniques used, GenAI outputs are only as good and reliable as their inputs — a contextualized, interconnected data foundation is critical. The adage, “garbage in, garbage out” still holds true in the GenAI era, and garbage-in can lead to perilous AI inaccuracies. The data foundation needs to allow GenAI applications to understand the context around the data. For example, the OT data from PLCs is usually tag data displaying vibration and temperature but does not have the context of what asset the PLC is in, which plant, line, material, or operation it is associated with.
“The development of multimodal foundation models is unlocking capabilities to turn not only text but also audio, images, and video into dynamically generated insights in the hands of frontline workers.”
Building a GenAI app for product design and manufacturing engineers regarding the optimal manufacturability (cost, quality, and delivery) requires an interconnected data foundation that includes the as-designed, as-planned, as-built, and as-used records of the product through its product life cycle. The opportunity for a product designer to design a better product lies in mining the actual history and experience through data gathered from users, and the IT and OT systems that span the engineering, manufacturing engineering, production execution and field services processes.
Start by Getting Your Data House in Order
Technology is a key pillar in the digital maturity journey, and RAG and prompt engineering are the first steps in understanding how GenAI can impact your business. A GenAI implementation should start with evaluating current digital maturity and focusing on the business outcome, starting small with high impact use cases, followed by an intentional plan to rapidly scale implementation and adoption of validated outcomes. As data privacy and security are top-of-mind in assessing new technologies, it is important to understand the data privacy policies of LLM service providers. From a technical perspective, the most crucial and foundational step is to build a contextualized, interconnected data foundation
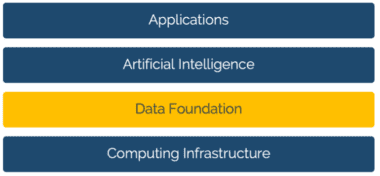
Figure 3: Illustrative architecture of applied AI
A four-layer framework illustrates the GenAI data foundation approach:
- The first layer is the hardware computing infrastructure layer.
- The second layer is the data foundation layer, which manages the engineering, operations, supply chain and financial activities and provides the domain-specific data, like real-time engineering and manufacturing information systems (IT), and operational technology (OT) like equipment, sensors, tools, and quality verification systems. This is where ERP, PLM and MES, play a role as the authoritative sources of business data, as well as an IIoT platform like PTC ThingWorx, play a role to get IT, OT and engineering technology data aligned and contextualized.
- The third layer is the AI technology layer and includes machine learning models, GenAI foundation models, orchestration services, etc. Examples of these include Azure OpenAI Service and Microsoft Copilot Studio for AI.
- The fourth layer is the applications layer, where the AI capabilities are applied to solve specific business problems, either as standalone applications or a plug-in of legacy applications.
GenAI represents a transformative opportunity for the manufacturing industry, poised to revolutionize data analysis, automation, and problem solving. Per World Economic Forum, GenAI is expected to add between $2.6 and $4.4 trillion in annual value to the global economy – nearly a quarter of which could be productivity improvements of up to two times and task automations of nearly 70% across manufacturing and supply chain-related activities6. Its potential to empower a wide range of the value chain is immense but realizing this potential hinges on high impact use cases and building a unified, contextualized, interconnected data foundation. We are just beginning to explore GenAI’s vast possibilities. Therefore, we encourage manufacturing companies to pull together a list of your most urgent, impactful business problems that require intensive data collection, validate the feasibility of the AI technology like RAG, and start with building your data foundation leveraging technologies like an IIoT platform and PLM. M
About the Authors:

Amol Adgaonkar is a Senior Director within the Worldwide Manufacturing & Mobility Industry team at Microsoft

Gonzalo Chavez is a Senior Analyst in Market Development, IoT at PTC

Howard Heppelmann is Divisional Vice President and General Manager of PTC’s ThingWorx IoT Solutions business segment

Alex Lemken is the Director of AI and Applied Analytics at PTC

James Zhang is the Vice President of Market Development, IoT at PTC
Appendix
1. BCG, December 2023 https://www.bcg.com/publications/2023/gen-ai-role-in-factory-of-future
2. Microsoft Cloud for Manufacturing, https://www.microsoft.com/en-us/industry/manufacturing/microsoft-cloud-for-manufacturing
3. The economic potential of generative AI. McKinsey. June 2023.
4. Top Innovative Technology Trends for Manufacturing Operations Leaders. Gartner. Nov 2023.
5. https://docs.llamaindex.ai/en/latest/getting_started/starter_example.html. LlamaIndex Starter Example.
6. Global Lighthouse Network: Adopting AI at Speed and Scale. World Economic Forum. Dec 2023
Dialogue: Manufacturing is Still a People Business
Rockwell Automation Chairman and CEO Blake Moret sees a highly automated future for plants and factories, but one in which simplification and empowering people with data-driven insights will be key.
In 1903, two years after Lynde Bradley invented the compression rheostat to control the speed of electric motors, he and Dr. Stanton Allen formed the Compression Rheostat Company. In 1909, the company was re-incorporated as the Allen-Bradley Company.
Decades of innovation followed, including the first solenoid starter with a single moving part, the incorporation of Allen-Bradley resistors in early mainframe computers, and the use of ferrite magnets in color televisions and computer memory cores.
In 1970, Allen-Bradley pioneered the programmable logic controller, and nine years later introduced Data Highway, the first plant floor network that replaced miles of wiring. In 1985, Rockwell International acquired Allen-Bradley, and in 2001 the company was officially renamed Rockwell Automation.
In February of this year, Rockwell Chairman and CEO Blake Moret sat down with the MLJ’s David R. Brousell to discuss industry trends, including the prospect of autonomous factory operations, the use of AI, and how advanced technologies may change the roles of manufacturing workers and leaders. This month, MLC members will tour Rockwell’s factory in Cleveland, Ohio, for a first-hand look at how Rockwell is running one of its own factories today.
Below are excerpts from the interview.
Q: MLC research into the effects of the pandemic clearly showed an acceleration of the adoption of digital and automation. Are you seeing that acceleration continuing or has it leveled off or entered a new phase?
A: I think that the acceleration has continued. During the pandemic, people had to innovate because you couldn’t have the same kind of mobility, the same number of people from lots of different companies collaborating. Applications like remote monitoring, the need for cybersecurity modeling, using digital twins — all of these concepts got turbocharged during the pandemic, and they continued as people needed to continue to innovate during subsequent supply chain shortages. So I think those things that people saw could be done and could be done at scale have continued.
The urgency that was created during the pandemic has really persisted. There is no turning back now. Everybody was hunkered down and thinking about how they could gain share and do things differently. And so that determination and that commitment has continued.
Q: You have been talking for some time about Rockwell’s mission as “creating the future of industrial operations”. At your November 8th Investor Conference in Boston, you said, regarding automation, that “people need to have superpowers” now in plants and factories. Talk a little bit about what that means, what your vision of a factory or plant is going into by 2030.
A: First of all, I think there will still be people in manufacturing plants. There are examples, of course, of lights-out factories, I don’t think that’s the end goal for the vast majority of manufacturers and their processes. Rather, it’s taking the people and freeing them up for the things that people are uniquely qualified to do and giving them data-driven insights so that they can use their decision-making powers to add innovation to processes but doing it working closely with the technology.
Q: I want to dig a little deeper into that question because the research we’ve been doing at MLC clearly shows that autonomous operations are on radar screens. In our Smart Factory Survey, the results of which we published in January. 48% of the respondents said that they are anticipating some degree of autonomous operations by 2030, with 12% of that group saying they’re expecting fully autonomous. Rockwell has been emphasizing autonomous production logistics. Do you think autonomous operations, although they could be technically feasible, are desirable?
A: I think we’re already seeing the benefits. If you think of traditional automation, that’s a portion of the autonomous operations equation in production, design, and control. That’s traditional automation — sensing, thinking, acting, taking inputs, interpreting them, and then changing the state of the final-mile devices. Add to that new forms of motion control or autonomous mobile robots, which is a big bet that Rockwell placed in the last few months, and you have a holistic view of what’s happening on the factory floor, along with people, of course. We’re already seeing companies across multiple industries making investments there, whether it’s the automotive industry, food and beverage, consumer packaged goods, life sciences, or in pharmaceuticals. All of them are seeing the opportunities in terms of the logistics of bringing material components to align and then taking finished goods away, moving it either to the loading dock or the warehouse. And above all of that, it’s the edge and the cloud information solutions to take all that data, bring it together, and give insights back to the people.
“I think AI has the opportunity to play a bigger and bigger role primarily to simplify the business of automation.”
Q: You mentioned the robotics side. Do you think the process side of the industry is further ahead compared to discrete?
A: I think that certain vertical industries have differing amounts of automation intensity. You can’t build a car, for instance, in discrete manufacturing without a high degree of automation, of programable controllers, robots and so on. In process, certainly control systems are managing the process loops, the integral safety as a part of that. When you think of a refinery or an ethylene cracker, there’s a certain amount of automation as well. Both have common threads. So there’s a need for open data exchange because there’s lots of different manufacturers represented on the floor, lots of different vintages of those products. And the ability to bring all that data together is a common need on both ends of the automation spectrum of applications.
But, there’s some basic common threads across all of those. And all of those industries see a need to simplify these processes because they all have a common need to be able to engage the broadest talent pool. And, of course, that talent pool in many cases has not more than a high school education.
And so the ability to provide technology that they’re comfortable interacting with and then the ability to grow during their careers is vitally important.
Q: Some people are saying that convergence is leading to the idea of data ecosystems. Do you think the ecosystem concept is something that’s going to actually take hold or are there too many issues around culture, around IP protection that are going to slow this down?
A: I think ecosystems are absolutely crucial and with industry-focused expertise represented within those ecosystems. If we talk about the technology of industrial operations or autonomous operations, there’s the expertise piece of it, the manufacturing lifecycle management that comes from people who are comfortable with these applications. And then there’s the ecosystem, because no one company is going to have all the answers.
When you think about the percentage that Scope 3 emissions play, it’s even more important to be able to assemble those industry-specific ecosystems. This may be the next frontier for us.
Q: You had a conversation at your recent Automation Fair with Microsoft’s Judson Althoff where he said “AI transformation succeeds digital transformation”. Do you agree with this idea? How significant a role do you think AI is going to have in manufacturers’ future operations and in how they think about their own competitiveness?
A: I think it’s a big deal. First, AI and its application in machine learning has been around for a while. A lot of the current press is around GenAI and ChatGPT-type language models. But the opportunity for self-learning, self-optimizing control systems has been around for a while and it’s having greater and greater impact.
In manufacturing, the ability to take difficult challenges in terms of process control, being able to look at areas where you relied in your plants on people with 30 and 40 years of experience who are now retiring, I think AI has the opportunity to play a bigger and bigger role there. We see it as primarily an opportunity to simplify the business of automation for our customers and for them to be able to engage a larger pool of workers as well as to reduce errors in standard, existing workflows.
There’s certainly a whole lot of internal processes in our own operations and in our own systems that can benefit from it. But I think we’re focusing first on what it can do for our customers.
“I do think that complexity is the primary deterrent to more rapid incorporation of technology in automation ….”
Q: What advice would you give to companies that are obviously aware of what’s going on but may not have stuck their big toe in the AI waters yet? How should they think about strategizing around AI and prioritizing investments?
A: Start with a well understood, finite problem that they have in their operations today. This is something that’s real, where they know that they’re going to get a big financial and/or time benefit by addressing it. Apply the resources on that problem, build the right team of experts, including everybody from the plant. People who are going to need to live with the incorporation of the new technology, to outside experts who can work well with their internal team. Get the benefits of that one challenge, and then expand it from there. And make sure the data is good.
Q: I was really thrilled when I heard you say simplification is going to sort out the winners and losers of this business in the next ten years because MLC has been focusing on the complexity issue. We’re very concerned that the more complex manufacturing companies get technologically, the harder it is to be resilient. How do manufacturers get the full benefits of often innovative, proprietary technologies that are coming out while at the same time avoiding the complexity that could lead to real daunting integration problems?
A: I think the simplification pertains to not just the technology, but the business model and the ecosystem as well. I do think that complexity is the primary deterrent to more rapid incorporation of technology in automation — whether it’s the way the pieces come together, the way that it’s required to maintain these systems, upgrade them, commission them, all throughout the lifecycle, and then the business models for being able to bring in the right technology and ensure that you’re getting the right support for it as well.
I think all of those aspects together point to the importance of simplification in these processes. That’s going to help us in the automation business to be able to see more rapid adoption of new technology.
Q: But simplification based on a rational architecture?
A: Yes. You do have to have that architectural component. Otherwise, you’ve got multiple architectures going on. Everybody gets into this journey at a different phase. They’re at a different point in time, and nobody is going to be able to adopt all the right technology, train the people in all the right areas, and to be able to say two or three or four years from now, we’re done.
It’s got to be a learning organization and, as you said, it requires an architecture that’s capable of ingesting new innovation as well. There’s a lot of new, innovative technologies coming at companies — whether it’s AR/VR, blockchain, or any of the technologies we associate with the emerging industrial metaverse set of technologies.
“Leaders need to have the ability to explain the why, to be able to recruit others to their cause at all levels of the organization.”
One of the biggest issues is just keeping up with the technology. But start with a problem that you understand. Don’t just go on a fishing trip. Start with something real. Solve a business problem.
Q: Thinking about the people who will occupy positions of leadership in the digital economy in the years ahead, what do you believe will be the most important characteristics that will define successful leadership of manufacturing companies as they become digital companies?
A: Well, let me start with what I don’t think is changing. I think that the leaders for today and tomorrow need to have a certain amount of experience, paying their dues with understanding what their processes are actually expected to accomplish. I don’t think there’s a magic formula. Even with all this new technology, leaders need to understand how things are being done and what the end goal is of their processes.
That being said, being comfortable dealing with volatility is key. What we have seen over the last few years are things that were never modeled before. Nobody did tabletop exercises to prepare for a lot of the things we’ve had to deal with. And so, you have to have a certain number of people who have the wiring to be, if not comfortable, at least understanding that this is a part of the job.
I think the other piece, as people managers, these leaders need to have the ability to explain the why, to be able to recruit others to their cause at all levels of the organization. That’s important. At the end of the day, it’s still a people business. M

FACT FILE: Rockwell Automation, Inc.
Location: Headquarters in Milwaukee, Wisconsin
Business Sector: Industrial automation and digital transformation
Revenues: $9 billion
Employees: 29,000
More than 100 countries
EXECUTIVE PROFILE: Blake Moret
Titles: Chairman and Chief Executive Officer, Rockwell Automation, Inc., and Chairman of the Rockwell Automation Charitable Corporation
Education: Bachelor’s degree in mechanical engineering, Georgia Tech
Industry Presence: Vice Chair, National Association of Manufacturers; member, Wisconsin Governor’s Council on Workforce Investment; co-chair of the World Economic Forum’s Advanced Manufacturing Community of CEOs; board member of the Business Roundtable; and board member of the Advanced Regenerative Medicine Institute (ARMI), Georgia Tech Advisory Board, FIRST Robotics, the United Way of Greater Milwaukee and Waukesha, and the Boys and Girls Club of Greater Milwaukee.
About the author:
David R. Brousell is Founder, Vice President, and Executive Director at the NAM’s Manufacturing Leadership Council.
Using Predictive Analytics to Improve Product Quality and Performance

Case study in how Nexteer is deploying predictive analytics to improve critical manufacturing processes, optimize production and reduce costs.
TAKEAWAYS:
● Collecting and analyzing data from sensors, machine logs and other sources can identify patterns and anomalies, enabling engineers to take proactive measures that prevent downtime, optimize production and reduce costs
● Predictive analytics can enhance communication and collaboration throughout a manufacturing operation.
● Harnessing the power of data and advanced analytics is key to Industry 4.0-level digital transformation.
Automotive steering and driveline product manufacturer Nexteer wanted to improve its critical manufacturing processes as part of its Industry 4.0 journey. As one step on that journey, the manufacturer turned to predictive analytics technology to improve the functional performance for its motion control systems and reduce the reject rate for end-of-line function testing. This project was selected as a finalist for the 2023 Manufacturing Leadership Award in the Engineering and Production Technology category.
The objective of the project, which kicked off in January 2020, was to develop and implement predictive analytics tools such as Big Data and machine learning technology to identify features that have an influence on end-of-line function testing. This is a complicated task, since a typical assembly can include thousands of features, including component dimensions, assembly parameters, and process parameters. One key aspect of the project was to install IIOT-based real-time vibration and force monitoring on critical components of its manufacturing process, with the goal of moving problem solving from a reactive to a proactive mode.

“By generating insights from data, the company was able to detect anomalies sooner, which led to … improved performance and reduced rejection rates.”
The result: By generating insights from data, the company was able to detect anomalies sooner, which led to earlier detection of machine issues, as well as improved performance and reduced rejection rates.
“As Nexteer advances its pursuit of increased business efficiency, it has recognized the limitations inherent in a reactive approach to problem-solving,” said Kevin Douglas, Executive Director, Global Manufacturing Engineering with Nexteer. “The necessity of transitioning to a proactive strategy is clear. This project shows Nexteer’s commitment towards a fully proactive future using Industry 4.0 transformation.”
Two Cases in Point
Nexteer made use of several technologies to identify the patterns and anomalies that will help engineers identify potential problems or inefficiencies in the production process. Here are two of the projects that used predictive analytics to improve performance and cost-effectiveness:
Project 1: Reduce the reject rates for end-of-line function tests
Solution: Machine learning algorithms were developed to identify factors that contribute to the end-of-line function tests. A machine learning dashboard incorporating a non-linear regression model predicted, with a 95% confidence interval, that modifications in these pivotal factors would substantially reduce the reject rates.
Result: Implementation of these data-driven recommendations led to a significant decrease in the reject rate, showcasing the efficacy of integrating machine learning techniques in optimizing production quality.
Project 2: Detect and diagnose machine problems causing quality issues with component manufacturing
Solution: The company designed a real-time system to monitor vibration and cutting forces during machining operations of critical components. The system was comprised of force and vibration sensors, an industrial computer running specialized software, and a connection to a secure business network for the transfer of vibration and force data to a database. They also developed web-based routines to analyze the vibration and force data, ensuring a comprehensive understanding of the machinery’s performance.
Result: Being able to quickly detect and diagnose machine problems before they resulted in increased reject rates resulted in lower operational costs and also enabled proactive machine maintenance.
Improving Crucial Business Metrics
One of the goals of the project was to improve first-time quality by reducing scrap and rework, as well as increasing productivity in high-growth markets. The superior performance of the product that resulted led to increased customer satisfaction and an increase in market share. Being able to collect and analyze data from IoT sensors and the company’s database, among other sources, provided valuable insights into the production processes and equipment performance, allowing for early detection of equipment failure or inefficiencies. This enabled engineers to take proactive measures to reduce downtime and optimize production.
In addition, having data readily available to plant floor personnel empowered operators, maintenance staff, and other production employees to quickly and effectively resolve problems before they became major issues — and improved collaboration and communication throughout the organization.

“Having data readily available to plant floor personnel empowered operators, maintenance staff, and other production employees to quickly and effectively resolve problems before they became major issues.”
Both the advanced analytics and IIOT technologies developed during the project now are being implemented in other critical manufacturing processes.
Steven Harris, Nexteer Vice President, Global Engineering, said, “In our journey towards Industry 4.0, Nexteer is harnessing the power of predictive analytics and Big Data, fundamentally transforming our manufacturing processes. Our goal was clear: enhance the functional performance of our systems and evolve from reactive to proactive problem-solving. This initiative has not only achieved our initial goals but also catalyzed productivity gains in key growth sectors. This success demonstrates our commitment to innovation and continuous improvement, setting a new standard in the automotive industry. Through this project, we are moving confidently forward, embodying the true spirit of Industry 4.0.” M

COMPANY FACT FILE
Name: Nexteer Automotive
Sector: Automotive
HQ location: Auburn Hills, MI
Revenues: $1 billion to $9.9 billion
Employees: 5,000 plus Employees
Web url: www.nexteer.com

Sue Pelletier is a contributing editor with the Manufacturing Leadership Journal.

Pravin Khurana, Ph.D. is Principal Manufacturing Engineer at Nexteer Automotive. He is responsible for leading IIOT and Advanced Data Analytics projects at Nexteer.
Digital Transformation Is Foundational for M4.0 Maturity

Manufacturers should prioritize data-driven decision-making and IT infrastructure.
TAKEAWAYS:
● Seventy-seven percent of respondents to an RSM survey said they plan to increase their information technology budgets in 2024.
● Middle-market organizations may have some catching up to do when it comes to digital transformation.
● Strategic investment in advanced technologies should be a priority.
Embracing digital transformation is more critical than ever for manufacturers, especially those in the middle market. That’s because midsize companies across the economy are poised to invest more in technologies central to digital transformation, according to data from the 2023 RSM US MMBI Digital Transformation Special Report, an RSM US Middle Market Business Index survey. For the survey, the Harris Poll interviewed 404 middle-market senior executives from a broad range of industries and sectors in April 2023.1 More than three-quarters (77 percent) of all MMBI survey respondents said they plan to increase their information technology (IT) budgets in 2024. Similarly, 74 percent of respondents indicated that digital transformation was the most important area or among the most important areas of investment for their companies.
Even with these priorities though, companies are not always clear about how to achieve their digital transformation goals, the survey found. According to the report, “Over half (52%) of all respondents have a clear and agreed-upon digital strategy that addresses their IT and digital transformation goals. But while one-third (33%) of all respondents have plenty of digital activities underway, they have not formalized their approach into a digital strategy.”
“Embracing digital transformation is more critical than ever for manufacturers, especially those in the middle market.”
For manufacturers, important factors behind a successful digital strategy include how organizations use data to drive decision-making, how they adopt advanced technologies in their supply chains, and how they prioritize enhancements that will make their IT infrastructure more resilient.
We examine some of the most important digital transformation considerations for manufacturers zeroing in on their journey toward M4.0 maturity.
Building a Digital Strategy
Manufacturers need to have technologies and processes in place that enable them to harness, filter, and analyze data with relative ease. This is foundational to digital transformation efforts, especially as factories become more connected with the use of Internet of Things (IoT)-enabled devices, sensors, and other machines. Governance, system architecture, and analytics are the three most critical data prongs for developing a strong digital strategy.
Data analytics in particular is central to helping manufacturers adapt to supply and demand changes, shifting geopolitical risks or myriad other ebbs and flows in the market. Analyzing sales, production, and supplier data can shed light on how customer preferences are changing, identify product backlogs, help with quality assurance, and more.
As noted in the RSM article “Modern manufacturing: Embracing the digital future,”2 “In truly digital factories, real-time metrics make adjusting to supply chain disruptions easier, connected devices make operations more seamless, and a variety of advanced technologies make scenario modeling more accurate.”
Manufacturers can tap into their data to develop comprehensive inventory dashboards, for instance, that can pull real-time information into one place. That can make it easier for companies to
- Monitor inventory, in terms of both quality and quantity;
- Adapt distribution and warehouse capacity as needed; and
- Forecast demand trends.
Artificial intelligence (AI) also offers many promising features like data analysis and financial forecasting to enhance efficiency, streamline processes, and improve decision-making.
At the time of the MMBI survey in April 2023, “Fewer than half of executives polled (44%) said they or someone they worked with had personal experience using ChatGPT or a similar generative AI platform,” Also noted in the report, “Broader company adoption was similar: Just 28% said their business was currently using AI and machine learning, and another 20% said they were planning on using it within the next year. Since that time, it would appear the adoption of this new technology has quickly risen, with numerous polls, news releases and public company earnings transcripts citing the ubiquity of AI.”
“Governance, system architecture, and analytics are the three most critical data prongs for developing a strong digital strategy.”
For many companies, though, digital transformation doesn’t mean upgrading platforms or using new technologies like generative AI. According to the MMBI report, “Many organizations are simply focused on securing their assets and strengthening their IT infrastructure.” In addition, “An overwhelming 88% of all respondents said they currently employ cybersecurity or data security in their businesses or plan to do so within the next 12 months, making it the most popular choice in the survey. Increased concern over cybersecurity was the top motivation respondents gave (65%) for changing their IT budgets.”
Manufacturers need to make sure their IT infrastructure is scalable and flexible for future growth. They also need to enhance it as needed to ensure compatibility with Industry 4.0 technologies that are becoming more common on factory floors and throughout operations.
Questions to Frame the Path Forward
Looking to the future, manufacturing leadership teams may find it useful to address these four questions to assess where they are and identify their ideal future state when it comes to digital transformation efforts:
- How are you evaluating your existing IT infrastructure and upgrades it may need to be able to support advanced technologies?
- Where might there be opportunities for your business to analyze data that are already at your fingertips?
- How are you making sure your leadership team is aligned on digital transformation priorities and implications across the organization?
- How might outsourcing some of your IT services help your broader digital transformation efforts?
If it feels like there is an overwhelming amount of work ahead for your business, know that it’s a common position. “Just over a third (38%) of respondents say they have substantially achieved their digital transformation goals,” the MMBI report said. “However, a slightly larger percentage (41%) say they are way off from achieving their digital transformation goals.”
Wherever your organization is on its digital maturity journey, it’s important not to lose sight of the fact that digital transformation will never truly be “finished.” Instead, consider it a constant evolution. M
Footnotes:
[1] Information from the RSM US Middle Market Business Index survey was originally published on RSMUS.com.
[2] This paragraph was originally published in the RSM article “Modern manufacturing: Embracing the digital future.”
About the authors:

Kendra Blacksher is a partner and industrials senior analyst at RSM US LLP.

Katie Landy is a principal and industrials senior analyst at RSM US LLP.
Ascending from Pilots to Manufacturing 4.0 Maturity

Tips for selecting, optimizing, and scaling digitalization initiatives across the enterprise
TAKEAWAYS:
● Manufacturers need to carefully evaluate compatibility, scalability, and trustworthiness when selecting digital solutions.
● Prioritizing effective digital transformation investments and executive support is crucial in this evolving landscape.
● Establishing a unified strategy owner can increase successful implementation and progress across the enterprise.
Personnel at all levels of manufacturing organizations are being tasked with “getting on board with the future,” often with little direction on what that really means and without a digital transformation leader providing a strategy or roadmap. As a result, lofty digitalization goals that begin as small-scale pilots may stall when gaps in understanding or planning exist, even if they yield great returns in isolation.
Aspirations for widespread Manufacturing 4.0 adoption are best served when there is clarity on where, when, and how to make technology investments as well as the larger implications on implementation, scalability, organizational change, and culture change. It is especially important in today’s environment of fast-moving and dynamically evolving innovations that are different from anything historically available to the industry.
Navigating Countless Technology Options
Myriad available software and technology solutions, at varying levels of maturity, offer the promise of advancing industrial digitalization goals. Informed consideration of whether a proposed technology initiative will “play nice” with another, deliver value, and scale adequately is necessary when choosing to make technology investments to optimize production and manufacturing performance.
Complicating matters are the newness of the digitalization market and the prevalence of:
- Niche technology providers: A multitude of niche players are still trying to determine where they fit in the larger market. This increases the burden on manufacturers trying to define what they need, who offers the solution, and how they can make it work with the technologies and digital infrastructure already in place.
- Venture capital startups: Very small startup companies often launch small-scale projects knowing they cannot, on their own, scale their business to develop at the rate their customers require. With a professional website, logo, and marketing material, they may appear to be a big player when they actually have few employees and customers. This does not make them irrelevant as they may have a solid vision of a wonderful product, but behind the scenes they are courting established solution providers for help penetrating the market, and some are fundamentally hoping to get bought out.
- Marketing ambiguity: Many digital solution providers present a general idea of the space they are in and the markets they serve, but their web pages and literature are not especially clear on what exactly they do and the solutions they provide. There may be talk of an ability to streamline certain processes and deliver some level or timing of ROI, and maybe a vague case study with a customer example, but there is little clarity on what the application actually does or how it works.
- Trust issues: For manufacturers and technology providers alike, it is difficult to know who you are doing business with these days unless you are dealing with an established, reputable company. There are empty promises when planned or in-development capabilities on a product roadmap never come to fruition. There are companies seeking demonstrations purely to validate their messaging or decision making rather than make commitments. And with very small startups, you do not really know what you are going to get or whether the company will be around for the long term.
Who Owns the Digital Transformation Strategy?
With all the complexities at stake, there remains a severe shortage of people who really understand how the puzzle pieces of a digital transformation strategy can fit together. Manufacturers rarely have a holistic internal roadmap or a single strategy owner who understands both information technology (IT) and operational technology (OT).
Granted, it is very common to see CTOs, CIOs, and IT organizations that are very capable and mature from an architecture standpoint. They have tried-and-true methodologies for ensuring their business infrastructure is technologically advanced and on the latest cloud-based platforms. And they have systems integrators or technology specialists providing solid insights related to IT enablement.
“Many manufacturers that have piloted limited initiatives are unsure how to measure success, and how to scale and integrate the solutions to execute on a daily basis.”
The gap in vision and execution, however, is at the factory floor level. There is not a lot of well-tenured expertise in how all the IT and OT pieces fit together within the rank and file of manufacturers, nor in the industry at large.
For instance, every original equipment manufacturer (OEM) has some sort of connected platform. There are third-party Industrial Internet of Things (IIoT) providers offering strategic solutions, such as sensor-based machine health monitoring and analytics from Advanced Technology Services (ATS). And there are different supervisory control and data acquisition (SCADA) platforms, data historians, and other enterprise resource planning (ERP) and enterprise asset management (EAM/CMMS) plugins. Whether and how these solutions are connected will impact asset reliability and operational performance.
Consequences In Change Management
When faced with an overwhelming disconnect in knowledge and lack of leadership on the strategy, manufacturers have difficulty seeing the big-picture vision and do not know how to make all the transformational technologies and processes work harmoniously. Consequently, many manufacturers that have piloted limited initiatives are unsure how to measure success, and how to scale and integrate the solutions to execute on a daily basis. Despite the hints of potential value, the lost progress and addition of manual work contribute to resistance to change.
How to Right the Ship
Since the root of the challenge is the lack of tenured understanding when it comes to digital transformation technology, it is critically important to have someone at an enterprise level leading the strategy who:
- understands the underlying architecture for the OT side of the business,
- knows how M4.0 digitalization and the IIoT fit into the overall operation,
- is open to new and different offerings and non-traditional ways of doing business,
- can decipher and assess prospective platforms and technologies, including smaller, newly built, and potentially insecure solutions,
- can articulate to stakeholders what the solution does, why it is needed, how it interrelates with existing solutions, and where it falls on the company’s roadmap to digital transformation, and
- is capable of merging the IT and OT technology pieces while ensuring the security protocols are what they need to be.
This individual and their assessment process for what is deployed to the factory floor is crucial to advancing beyond discrete pilot tests to M4.0 maturity. They can prioritize scalable, effective digital transformation investments by establishing where the real opportunities lie, developing a business case, understanding the budget and the return expected from the solution, and determining which vendor(s) can deliver on the goal.
Fortunately, gaining executive support is less of a challenge today. Not long ago, the earliest drivers and adopters of advanced technologies were often forward-thinking engineers. That has since shifted with the C-suite now focusing on digital transformation as a competitive advantage. Increasingly, technology enhancements are pre-approved, in the budget, and part of the plan. What may be lacking is executive direction unless there is someone bridging the knowledge gap between the factory floor and the executive office.
How Partners Can Help
When expertise is lacking in house, being open to partnering with strategic technology and service providers can turn the tide in digital transformation success. Instead of making a “build versus buy” decision, a bit of both is needed. Ultimately, any technology enhancements must live within an infrastructure that suits your enterprise integration, security, and data attribute requirements.
Expert technology and service providers can help facilitate digital transformation planning and close knowledge gaps. ATS does this by bringing their solutioning specialists to even the earliest customer engagements. Being on the front line allows them to better extract customer requirements, articulate new solutions that will work with existing solutions, anticipate future needs, and prioritize the integration of capabilities from a product management standpoint. They can also coach customers through what the potential could be and how you might work together.
“The earliest drivers of advanced technologies were often forward-thinking engineers. That has since shifted with the C-suite now focusing on digital transformation.”
Partnering can also lead to the service provider extending the value of existing customer investments. Incorporating a customer’s small-scale successes into the provider’s larger digitalization solution makes them scalable across the enterprise.
An example is predictive maintenance, which is the proven strategy for improving uptime by detecting and correcting degrading asset conditions before failure occurs. In one use case, ATS helped protect a packaging manufacturer’s plant maintenance team from being overwhelmed by massive and growing volumes of data by automating the collection of machine sensor data and centralizing it for expert analysis and prescriptive recommendations. This allowed the manufacturer to meet reliability and performance objectives more efficiently and effectively.
Finally, it is important to remember that there is no magic bullet in digital transformation. In this example, automating data gathering and analysis does not replace maintenance best practices or standard work. If nobody acknowledges the alert of impending failure or executes the recommended actions, the asset will still fail. Make sure that processes for planning and scheduling corrective actions and closing the loop afterward continue to be followed. M
About the Author:

Micah Statler is Director of Industrial Technologies at Advanced Technology Services.